E-Learner Authentication
 On Friday at WCET, I attended a session where two presenters had radically different approaches for tackling the student authentication “problem” in distance education. It was exactly one year ago at the WCET conference in San Fran when Steven Crow of the Higher Learning Commission put a scare into the audience by saying that Congress was poised to include harsh distance education requirements into the Higher Ed Reauthorization Act. He was right at the time, but then Congress backed off (temporarily?) and passed a partial law dealing with the financial parts of the Act, but held off on the academic parts.
On Friday at WCET, I attended a session where two presenters had radically different approaches for tackling the student authentication “problem” in distance education. It was exactly one year ago at the WCET conference in San Fran when Steven Crow of the Higher Learning Commission put a scare into the audience by saying that Congress was poised to include harsh distance education requirements into the Higher Ed Reauthorization Act. He was right at the time, but then Congress backed off (temporarily?) and passed a partial law dealing with the financial parts of the Act, but held off on the academic parts.However, this age-old question for e-learning still lingers:“How do you know that it really is Billy Bob at the end of the fiber optics who is taking the exam?” I’ve never worried too much about this question, because I really don’t believe that it is that much of an issue. However, Congress and now the accrediting bodies seem to be zeroing in on this question, so I do think that we will soon be required to have some sort of plan in place to attempt to authenticate the distance learners in one or more ways.
Some of the basic authentication techniques include:
- Who we are: fingerprint biometrics, iris scans, voice prints, DNA, etc.
- What we have: Drivers License, Passport, Digital Tokens, etc.
- Where we are: IP address, phone calls, video monitoring, etc.
- What we know: personal data about our past

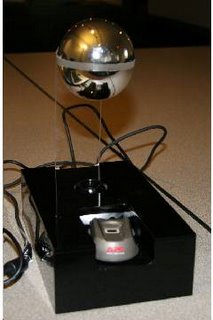
- The device includes a camera, microphone, and biometric reader (finger scan)
- The device software evaluates input and compares to a pre-set threshold for sound and movement
- Excessive movement or noise activates the camera and microphone
- The device only records selected threshold activities (too much noise or too much movement provides a flag on that student)
The other approach for identity verification was described by Mike Jortberg of Acxiom Data Solutions. This personal information approach is used extensively in Financial Services. The information is portable, is not limited by location or channel, and no hardware is required.
Acxiom has created a monstrous database using publicly available data. The data comes from over 70 database sources of public records such as marriages, first births, work retirements, residential moves, divorces, etc. Acxiom “touches” those data sources 3 billion times a day to constantly have the most up-to-date information. Does that seem excessive? Not if you consider that there are 155,000 changes per day in this data as people get married, divorced, etc. etc.
The idea here is that students would need to answer one or more personal questions at various “trigger events;” such as at registration, exams, paper submissions, or other significant online course events and work completion events. Examples of questions include the following: a) on which of these streets have you lived previously, b) what is the street number of your most previous address, and c) which of these is one of your previous employers? These are multiple choice questions to help guard against the type of brain freeze that prevents some people from remembering their own phone number when under pressure.
If we have to go down one of these roads, I guess I would prefer the second, gentler approach. But just barely. They're both creepy as hell if you ask me. The first one seems so invasive and so much like Big Brother. I know that second one will be easier for students to get around if they want to cheat, but let's face it ... if someone is committed to cheating, then even the sledgehammer approach of THE DEVICE probably won't stop them.Technorati Tags: cheating, eLearning, WCET


Comments